[ad_1]
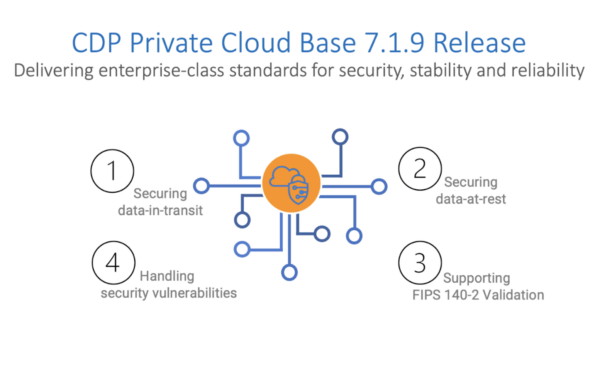
As knowledge ecosystems evolve safety turns into a paramount concern, particularly throughout the realm of personal cloud environments. Cloudera on Personal Cloud with the Personal Cloud Base (CDP PvC Base) stands as a beacon of innovation within the realm of information safety, providing a holistic suite of options that work in live performance to safeguard delicate data. With the newest 7.1.9 launch, the journey in direction of a safer knowledge ecosystem continues—one the place companies can unlock the complete potential of their knowledge with peace of thoughts.
How does this launch elevate safety?
Cloudera on personal cloud integrates a unified safety platform that orchestrates the complete spectrum of safety measures. From entry controls and id administration to encryption and auditing, this complete strategy ensures that each aspect of your knowledge ecosystem is protected towards potential threats and vulnerabilities. This newest model delivers safety enhancements for knowledge at relaxation, knowledge in transit, and Federal Data Processing Requirements (FIPS) compliance, in addition to compliance with varied regulatory necessities.
Platform safety for knowledge in transit
The platform makes use of transport layer safety (TLS) and safe socket layer (SSL) protocols to ascertain a safe communication channel between totally different parts of the platform for higher privateness and knowledge integrity. Utilizing a cryptographic protocol safeguards knowledge from being intercepted or modified throughout transit, thwarting potential cyber threats. Subsequently, it’s essential to replace safety protocols to adapt to the altering risk panorama and defend towards the newest assault strategies.
This model securely leaps ahead by providing TLS model 1.2, which delivers a refined set of cipher suites, strengthened cryptographic algorithms, and a strong handshake course of for improved safety and resilience. Moreover, the discharge introduces Oracle TCP/IP utilizing SSL (TCPS) help to facilitate safe communication between PvC Base parts and Oracle backend DB. This ensures knowledge administration and monitoring occurs securely by the TCPS connection protocol.
Enhancing encryption for knowledge at relaxation
A number of knowledge at relaxation encryption mechanisms akin to key administration programs (KMS) make sure that delicate data is shielded from potential threats and unauthorized entry. The most recent launch makes use of Ranger KMS to supply unified key administration companies for encryption in lieu of key trustee server (KTS). This enhances buyer expertise, as this centralized strategy streamlines coverage administration and ensures consistency in entry management guidelines. Moreover, for current customers of KTS, import of keys from KTS and NavEncrypt in addition to automation of NavEncrypt nodes from previous KTS servers to Ranger KMS servers has been streamlined so knowledge encryption and safety stays uncompromised.
On this newest model, perimeter safety is enhanced as properly. The Knox HttpFS characteristic offers a safe solution to entry HDFS assets by an internet interface utilizing HTTP strategies. Moreover, Knox token authentication can now be used to ascertain safe connections and handle consumer entry. Token-based authentication offers environment friendly and scalable consumer authentication utilizing tokens, that are simply rolled, renewed, and revoked and due to this fact, cut back the danger of publicity of consumer credentials.
Customized Kerberos principals and repair customers
Isolation is a crucial idea when securing infrastructure to attenuate the potential impression of vulnerabilities. At present, CDP companies use default names for Kerberos principals with matching service consumer names on host machines. Nevertheless, utilizing the default configuration can prolong the accessibility of a single service past the cluster it’s put in on in a multi-cluster deployment. To handle this, organizations in search of extra superior strategies for segregating a number of clusters can create customized Kerberos principals (CKP) together with corresponding customized service customers. The CKP empowers organizations to limit companies from accessing knowledge on clusters belonging to distinct traces of enterprise or initiatives. It’s value noting that customers achieve entry to this performance through the course of of making a brand new cluster or including a service to an current cluster.
FIPS 140-2 updates
For organizations entrusted with confidential monetary knowledge, healthcare data, or authorities data, adherence to rigorous safety requirements like FIPS shouldn’t be solely a strategic selection but additionally a authorized obligation.
Configuring the discharge to make use of FIPS 140-2 compliant cryptography inside an working system (OS) configured for FIPS-mode is at present supported for patrons deploying on RHEL 7.8 and seven.9. With the addition of Purple Hat Enterprise Linux (RHEL) 8.8 FIPS help, prospects utilizing RHEL 8.8 can now deploy the platform configured to make use of FIPS 140-2 compliant cryptography, on an FIPS-mode enabled RHEL 8.8 working system. There are a variety of CDP parts that help configurability to make use of FIPS 140-2 compliant cryptography at this time. Nevertheless, as a part of our efforts to remain steadfastly aligned with the best safety benchmarks, we’ve got prolonged the configurability to make use of FIPS 140-2 compliant cryptography help with the Phoenix, NavEncrypt, Ranger Key Administration Service, and Key Trustee Server parts. Full record of supported parts for FIPS 140-2 can be found on the required stipulations for FIPS for CDP web page.
Safety vulnerabilities remediation
We take fixing safety vulnerabilities severely! We’ve an efficient vulnerability remediation course of that proactively scans, prioritizes, fixes, and screens frequent vulnerabilities and exposures (CVE) to display our dedication to our prospects’ safety. The 7.1.9 launch improved platform safety and InfoSec compliance with 100+ resolved essential CVEs. This reduces the assault floor in buyer deployments for a safer ecosystem that forestalls vulnerabilities from being exploited at any level.
Conclusion
On this world of technological evolution and the ever-changing panorama of cybersecurity, the proactive effort to maintain safety protocols updated is essential. By imposing sturdy encryption mechanisms for knowledge at relaxation, knowledge in transit for enterprises, and supporting CGI requirements for regulated industries, Cloudera on personal cloud demonstrates a dedication to sustaining the integrity and availability of their programs and data.
Allow us to empower your group to navigate the cybersecurity panorama confidently and successfully with this newest launch! For those who’re not already on the newest launch, get began at this time! It’s now simpler than ever to improve or migrate from earlier variations to this one. To seek out your good path to 7.1.9, click on on our migration and improve information.
[ad_2]
