[ad_1]
Apple units use many frequent web safety requirements. This is what every of them does, and methods to use them in your Apple {hardware}.
Within the networked world we dwell in, web connectivity is ubiquitous.
Maintaining community communications safe is without doubt one of the most essential facets of web know-how. Over the many years, a number of totally different requirements have advanced to maintain networks and units safe.
On this article we’ll have a look at a number of of those requirements, and the way they relate to Apple units.
IPsec, IKEv2, L2TP
Three key applied sciences are used for safe connections and VPNs: IPsec, IKEv2, and L2TP.
IPSec is a safety normal which was born of early DARPA ARPANET analysis. It was later formalized by MIT, Motorola, and NIST.
IPSec is usually utilized by VPNs, offering safe authentication, key alternate, encryption, and information integrity capabilities. In the event you’ve ever put in VPN software program on one in every of your Apple units, you have used IPSec.
It’s thought of a “Layer 3” protocol which sits atop Layer 2 protocols, which we’ll see in a second.
IKEv2 is the Web Key Trade protocol. There are three variations this protocol: IKE, IKEv1, and IKEv2.
It’s utilized in IPSec and by DNS to create and alternate safe key pairs throughout connections. Shared keys are a part of Public Key Infrastructure (PKI) which eliminates the necessity for passwords.
IKE is predicated on two earlier protocols: The Oakley protocol and ISAKMP. These protocols got here out of efforts within the late 1990’s to safe web connections when it grew to become clear early web communications had been insecure in lots of situations.
The Oakley protocol makes use of the now-famous Diffie-Helman Key Trade algorithm to securely alternate keys for encryption.
ISAKMP is a key alternate framework that gives a safety affiliation and keys for use by key alternate protocols similar to IKE. Cisco adopted each the Oakley and ISAKMP protocols to be used in most of its VPN and router merchandise.
There are different key alternate protocols, similar to Kerberized Web Negotiation of Keys (KINK) and SKEME.
L2TP, or Layer 2 Tunneling Protocol is a tunneling protocol used for management messages throughout community communication. L2TP does not safe or encrypt information or content material itself, it solely encrypts the management alerts utilized in connections.
This protocol was formalized in 1999 within the RFC 2661 specification which was shaped because of Cisco’s L2F protocol and Microsoft’s PPTP protocol. It additionally makes use of the Consumer Datagram Protocol (UDP) throughout packet transmission.
UDP has the primary benefit of being an acknowledgment-free broadcast protocol, for which listeners wait on a sure port for info with out having to answer to the sender.
L2TP happened as a necessity for safety for PPP (Level-To-Level Protocol) when dial-up modems had been nonetheless in widespread use. Information packets could be transmitted over a Layer 2 tunnel through the use of one of many different extra encrypted protocols.
Safe tunneling ensures any information touring within the tunnel is encrypted and managed between solely two factors. This makes replay and man-in-the-middle assaults tough for attackers to execute.
L2TP is used largely in company VPNs for safe entry.
Many VPN apps can be found for Apple units, through the App Retailer. Most Apple working programs additionally present built-in options for simply including VPN profiles to units.
IPsec, IKEv2, and L2TP function largely behind the scenes, and except there’s some particular setting it’s essential change, you will often by no means have to trouble your self with them.
TLS, SSL, and X.509 certs
When the net first went mainstream within the late Nineties, it shortly grew to become obvious that each one internet communication wanted to be encrypted. All in order that information could not be intercepted and listened to between browsers and servers.
Consequently Safe Sockets Layer (SSL) was developed. Now referred to as Transport Layer Safety, this protocol encrypts most visitors between internet browsers and servers.
The “s” in “https” stands for “safe” – and signifies that you’re searching a web site through a safe connection.
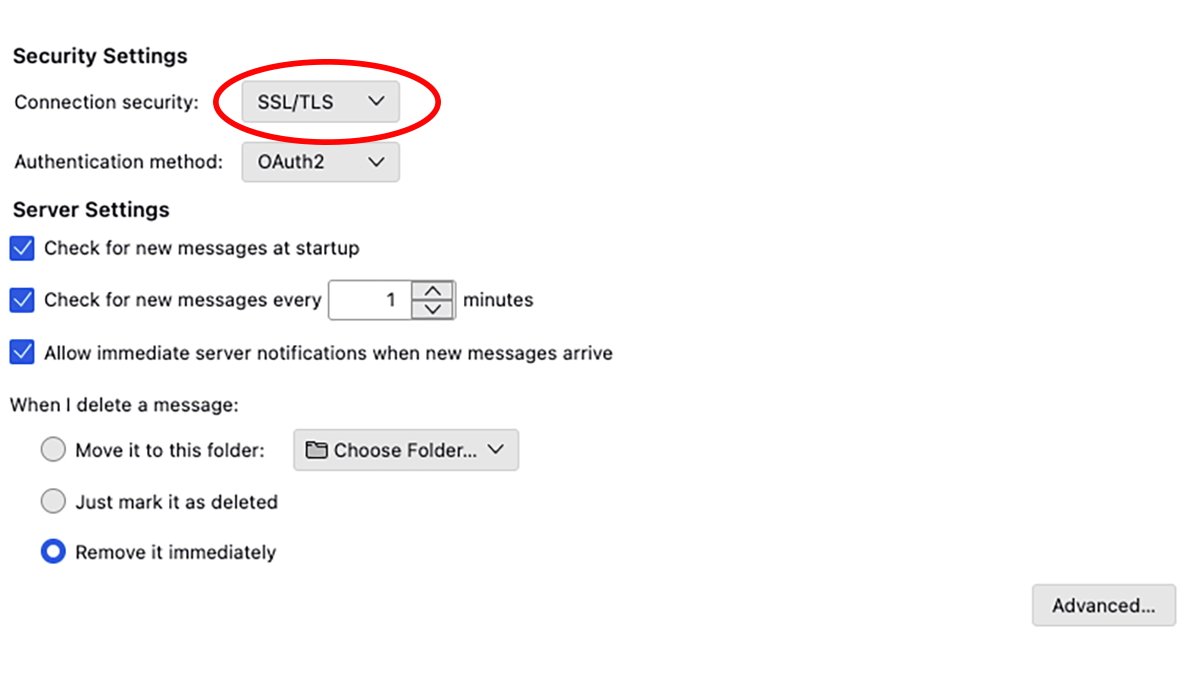
SSL/TLS may also be utilized in some safe e-mail communications. TLS was additionally proposed in 1999 and has undergone three revisions, the present model of which is TLS 1.3.
SSL was initially developed in 1994 for the primary variations of Netscape’s Navigator browser, which at this time has morphed into Mozilla Firefox. There’s additionally a Datagram Transport Layer Safety (DTLS) protocol.
TLS makes use of X.509 certificates to alternate info utilizing encryption and encrypted handshakes. As soon as the handshake completes, the server often offers the shopper app with a certificates so sever could be trusted.
X.509 certificates permit a shopper app to confirm the authenticity of the server, in order that impersonation assaults cannot work. The X.509 normal is outlined in RFC 5280 by the Worldwide Telecommunications Union (ITU).
The foremost good thing about TLS is that it prevents anybody who is likely to be listening in on the information alternate from with the ability to learn the information within the clear. All as a consequence of it being encrypted.
Most often, trendy Apple units and most software program operating on Apple units robotically know methods to use TLS, so that you should not want to fret about it. So long as you utilize an “https” connection when searching the net, TLS is automated.
Some e-mail shopper apps similar to Mozilla Thunderbird mean you can specify TLS/SSL because the communication safety normal:
WPA/WPA2/WPA3 Enterprise and 802.1X
When WiFi networking first appeared on the finish of the final century, a brand new safety normal, WEP (Wired Equivalency Privateness) was developed to permit wi-fi networks to connect with different units securely.
WEP had critical safety flaws, and in response, Wi-Fi Protected Entry (WPA) was produced. This protocol has undergone three revisions for the reason that early 2000s, with the present model being WPA3.
Most trendy WiFi units, together with Apple’s units, present WEP3 for connections.
Each Apple’s WiFi and Ethernet units additionally present for connections that use one other safety protocol referred to as 802.1X. This protocol is a part of the 802 community normal as outlined by IEEE, which covers each WiFi and Ethernet wired networks.
802.1X prevents a sort of community assault often known as {Hardware} Addition, the place a malicious gadget is used to connect to a community and carry out hacking actions. For instance, a small laptop like a Raspberry Pi plugged right into a spare community port.
By way of the usage of an authentication server, 802.1X can often thwart such assaults by authenticating the person through WiFi, LAN, or WAN.
In at this time’s world of units in every single place, {Hardware} Addition assaults are rather more frequent than they was once.
WPA is not supported by modem variations of Apple’s working programs, so usually, you will need to use WPA2, WPA3, or some variant thereof.
Login Window Mode (LWM) is a means to connect with a safe community from the Mac’s login window if the community helps Listing Companies.
With a view to use LWM, you want a connection to an Lively Listing or Open Listing server. Additionally, you will want an put in Mac community configuration profile which permits LWM for the community you are making an attempt to connect with.
As soon as configured, on the Mac Login Window, choose Different from the record of customers, then enter your Listing Companies person identify and password. From the popup menu, choose the community interface you need to join on (WiFi or Ethernet).
Lively Listing and Open Listing are applied sciences that permit person info and credentials to be saved on a central server for authentication. We’ll cowl Open Listing in an article within the close to future.
Most often, Apple has made community safety seamless so that you often will not want to fret about it. The above applied sciences are largely all a part of internet or web requirements, and in most software program their use is automated.
[ad_2]